Introduction
Amazon Web Services (AWS) powers a huge portion of modern infrastructure — but with flexibility comes risk. Many security incidents in the cloud are not due to AWS itself, but misconfigurations and poor security practices.
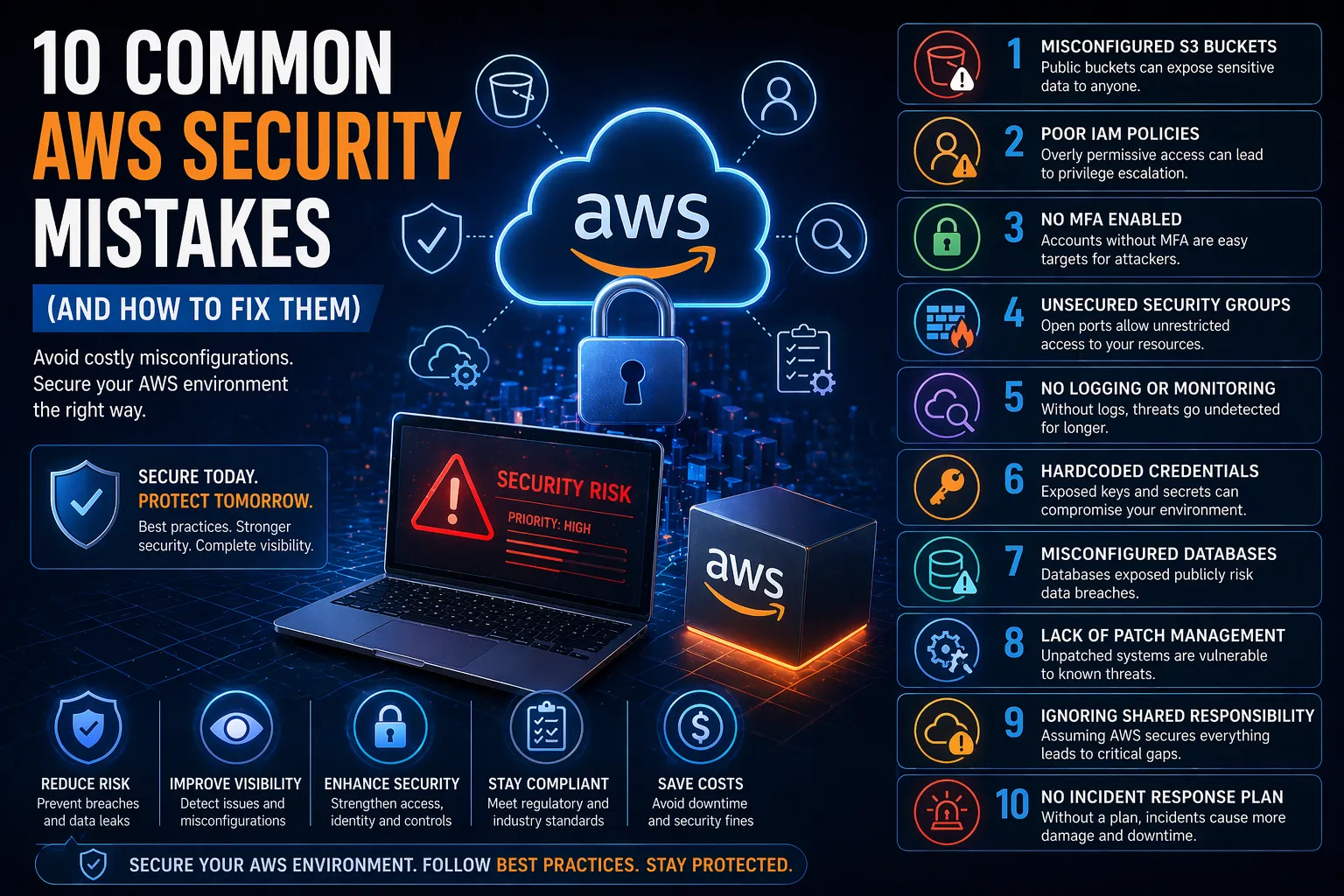
So what are the most common AWS security mistakes, and how can you avoid them?
This guide breaks down the biggest risks and how to fix them before they lead to breaches.
Why AWS Security Mistakes Happen
AWS operates under a shared responsibility model:
- AWS secures the cloud infrastructure
- You are responsible for securing what you put in the cloud
Most security issues occur when organisations misunderstand this model or fail to implement proper controls.
1. Misconfigured S3 Buckets
The Problem
Publicly exposed S3 buckets are one of the most common AWS security mistakes, often leading to data leaks.
The Risk
Sensitive data becomes accessible to anyone on the internet.
How to Fix It
- Disable public access by default
- Use bucket policies and IAM controls
- Enable logging and monitoring
2. Poor Identity and Access Management (IAM)
The Problem
Overly permissive roles and excessive user privileges.
The Risk
Attackers can escalate privileges and access critical systems.
How to Fix It
- Apply least privilege access
- Use role-based access instead of shared accounts
- Regularly audit IAM policies
3. Lack of Multi-Factor Authentication (MFA)
The Problem
Accounts protected only by passwords.
The Risk
Credential theft can lead to full account compromise.
How to Fix It
- Enforce MFA for all users
- Especially for admin and root accounts
4. Unsecured Security Groups
The Problem
Open ports (e.g. 0.0.0.0/0) exposing services to the internet.
The Risk
Attackers can directly access servers and applications.
How to Fix It
- Restrict IP ranges
- Use private networks where possible
- Regularly review firewall rules
5. No Logging or Monitoring
The Problem
Lack of visibility into activity across AWS environments.
The Risk
Breaches go undetected for extended periods.
How to Fix It
- Enable AWS CloudTrail
- Use CloudWatch for monitoring
- Implement alerting for suspicious activity
6. Hardcoded Credentials
The Problem
API keys and secrets stored in code or repositories.
The Risk
Attackers can gain direct access to AWS services.
How to Fix It
- Use AWS Secrets Manager or Parameter Store
- Rotate credentials regularly
- Avoid storing secrets in code
7. Misconfigured Storage and Databases
The Problem
Databases and storage services exposed without proper controls.
The Risk
Sensitive data exposure and compliance violations.
How to Fix It
- Restrict access using IAM and network controls
- Encrypt data at rest and in transit
- Regularly audit configurations
8. Lack of Patch Management
The Problem
Outdated instances and unpatched systems.
The Risk
Known vulnerabilities can be exploited.
How to Fix It
- Regularly update systems
- Automate patching where possible
- Use vulnerability scanning
9. Overlooking the Shared Responsibility Model
The Problem
Assuming AWS handles all security.
The Risk
Critical gaps in application and data protection.
How to Fix It
- Understand AWS responsibilities vs yours
- Implement security controls at every layer
10. No Incident Response Plan
The Problem
No defined process for responding to breaches.
The Risk
Delayed response increases impact and damage.
How to Fix It
- Develop an incident response plan
- Test it regularly
- Ensure clear roles and responsibilities
How to Prevent AWS Security Mistakes
To reduce risk, organisations should:
- Regularly audit cloud configurations
- Implement continuous monitoring
- Use automated security tools
- Follow best practice frameworks
Most importantly, security should be built into your cloud environment from the start — not added later.
If you’re looking to secure your AWS environment properly, integrating these controls into a broader Cloud Security strategy is essential.
Conclusion
AWS is secure by design — but only if configured correctly.
The most common AWS security mistakes are preventable with the right controls, visibility and processes.
By addressing these risks early, organisations can:
- Protect sensitive data
- Reduce breach risk
- Maintain compliance
- Strengthen overall cloud security
FAQs
What are the most common AWS security mistakes?
Misconfigured S3 buckets, poor IAM policies, lack of MFA, and insufficient monitoring are among the most common.
Is AWS secure by default?
AWS infrastructure is secure, but customers must configure their environments properly.
What is the biggest AWS security risk?
Misconfiguration — particularly public exposure of data and services.
How do you secure AWS environments?
Through proper IAM controls, monitoring, encryption, and continuous security assessments.