Introduction
As cyber attacks become more advanced, gaining initial access is often just the beginning. Once inside a network, attackers don’t stop — they move deeper to find sensitive systems, data and privileged accounts.
This is known as lateral movement, and it’s one of the most dangerous stages of a cyber attack.
So, what is lateral movement in a cyber attack, and how does it work?
This guide explains how attackers move through networks, the techniques they use, and how organisations can stop them.
Lateral Movement Explained
Lateral movement in a cyber attack refers to the techniques attackers use to move from one system to another after gaining initial access.
Instead of staying on a single compromised machine, attackers expand their reach to:
- Access sensitive data
- Escalate privileges
- Compromise critical systems
- Maintain persistence within the network
This allows attackers to maximise impact and avoid detection.
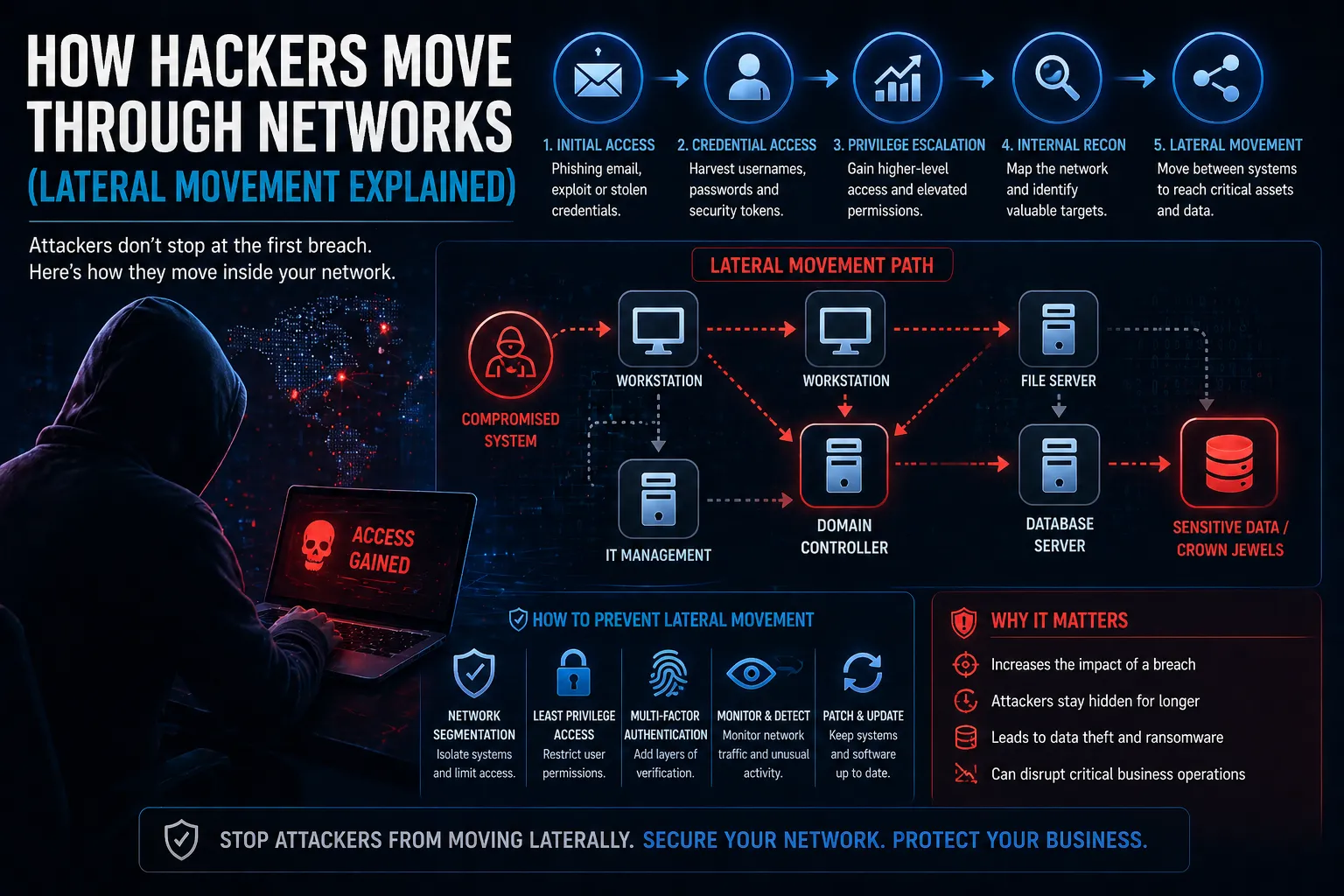
How Lateral Movement Works
Once inside a network, attackers follow a structured approach to move across systems.
Typical stages include:
- Initial compromise – Gaining access via phishing, exploits or stolen credentials
- Credential harvesting – Collecting usernames, passwords or tokens
- Privilege escalation – Gaining higher-level access
- Internal reconnaissance – Mapping the network and identifying targets
- Lateral movement – Moving between systems
This process continues until attackers reach high-value assets.
Common Lateral Movement Techniques
Attackers use a variety of tools and methods to move through networks.
Examples include:
- Pass-the-Hash – Using stolen password hashes to authenticate
- Remote Desktop Protocol (RDP) – Accessing systems remotely
- PsExec – Executing commands on remote machines
- Credential dumping – Extracting login details from memory
- Exploiting trust relationships – Moving between connected systems
These techniques allow attackers to blend in with normal network activity.
Why Lateral Movement Matters
Lateral movement significantly increases the impact of a cyber attack.
Without controls in place, attackers can move freely across systems.
Key risks:
- Wider breach impact – More systems become compromised
- Data exfiltration – Sensitive data is accessed and stolen
- Privilege escalation – Attackers gain admin-level control
- Longer dwell time – Attacks go undetected for longer
How to Detect Lateral Movement
Detecting lateral movement requires visibility across your network.
Key indicators include:
- Unusual login activity
- Access from unexpected locations
- Multiple failed login attempts
- Unusual internal traffic patterns
- Unexpected privilege escalation
Monitoring these signals helps identify attackers before they reach critical systems.
How to Prevent Lateral Movement
Preventing lateral movement requires a layered security approach.
- Implement network segmentation
- Apply least privilege access controls
- Use multi-factor authentication (MFA)
- Monitor network activity continuously
- Secure credentials and rotate regularly
- Patch vulnerabilities promptly
These controls limit how far attackers can move within your environment.
Lateral Movement and Cyber Security Strategy
Lateral movement is a key focus in modern cyber security strategies.
It is addressed through:
- Network Security controls and segmentation
- Incident Response planning and containment
- Threat detection and monitoring
- Identity and access management
Combining these controls reduces the likelihood and impact of lateral movement attacks.
Conclusion
So, what is lateral movement in a cyber attack?
It’s the process attackers use to move through networks after gaining access, allowing them to expand control and reach critical systems.
By understanding how lateral movement works, organisations can:
- Detect threats earlier
- Limit breach impact
- Protect sensitive systems
- Strengthen overall cyber resilience
FAQs
What is lateral movement in cyber security?
It is when attackers move between systems within a network after gaining initial access.
Why is lateral movement dangerous?
It allows attackers to spread across systems, access sensitive data and escalate privileges.
How do attackers move laterally?
They use techniques like credential theft, RDP access and exploiting trust relationships.
How do you stop lateral movement?
By using network segmentation, monitoring, MFA and strong access controls.

Leave a Reply