Introduction
Cloud environments offer flexibility, scalability and efficiency — but they also introduce new security risks. One of the most common causes of cloud security breaches is cloud misconfiguration.
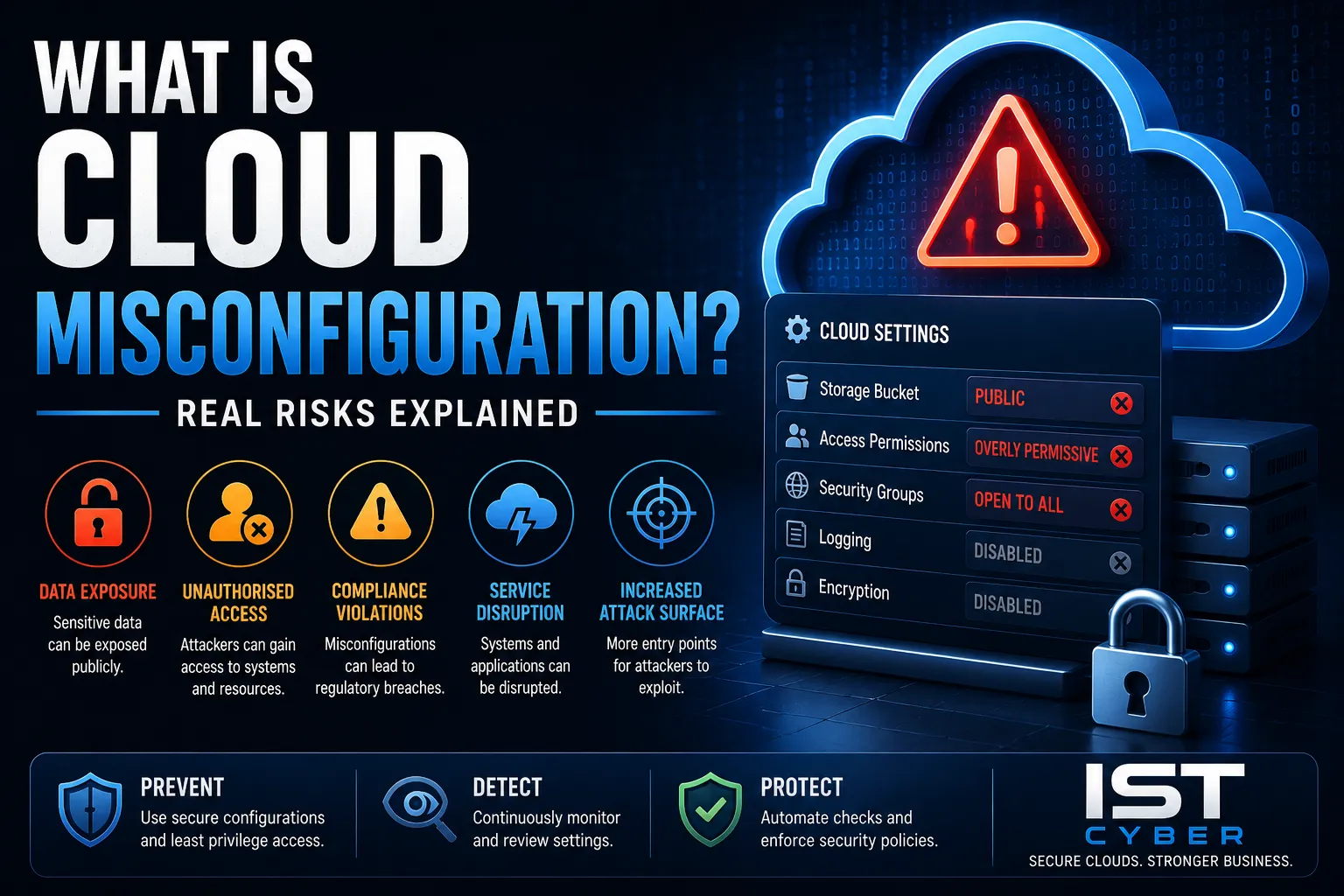
Simple mistakes in cloud settings can expose sensitive data, weaken security controls and create opportunities for attackers.
So, what is cloud misconfiguration, and why is it such a serious risk?
This guide explains how cloud misconfigurations happen, the real risks involved and how businesses can prevent them.
Cloud Misconfiguration Explained
Cloud misconfiguration occurs when cloud systems, services or resources are configured incorrectly, creating security weaknesses or exposing sensitive data.
Examples include:
- Publicly exposed storage buckets
- Weak access permissions
- Disabled security controls
- Unsecured APIs and ports
These mistakes are one of the leading causes of cloud-related breaches.
How Cloud Misconfigurations Happen
Cloud environments are highly complex and constantly changing.
Common causes include:
- Human error
- Lack of visibility across cloud assets
- Poor access management
- Misunderstanding the shared responsibility model
- Rapid deployments without security reviews
Without proper governance, these risks increase significantly.
Real Risks of Cloud Misconfiguration
1. Data Exposure
Misconfigured storage or permissions can expose sensitive data publicly.
2. Unauthorised Access
Weak identity and access controls may allow attackers to gain access.
3. Compliance Violations
Improperly secured cloud environments can breach regulatory requirements.
4. Service Disruption
Attackers may exploit misconfigurations to disrupt systems and operations.
5. Increased Attack Surface
Unsecured cloud resources provide additional entry points for attackers.
Examples of Common Cloud Misconfigurations
Public Storage Buckets
Cloud storage accidentally configured for public access.
Overly Permissive IAM Policies
Users or applications granted excessive permissions.
Open Security Groups or Firewalls
Unrestricted access to cloud systems from the internet.
Disabled Logging and Monitoring
Lack of visibility into suspicious activity and threats.
Default Credentials
Using weak or unchanged default passwords and settings.
Why Cloud Misconfiguration is So Common
Cloud environments move quickly, and security is often overlooked during deployment.
Contributing factors:
- Rapid cloud adoption
- Complex multi-cloud environments
- Skills shortages
- Lack of automated security controls
These factors make cloud security management challenging for many organisations.
How to Prevent Cloud Misconfiguration
- Implement least privilege access controls
- Use secure baseline configurations
- Enable continuous monitoring and logging
- Perform regular cloud security assessments
- Automate configuration reviews where possible
- Train staff on cloud security best practices
Proactive management is essential for reducing cloud risk.
How This Fits into Cyber Security Strategy
Preventing cloud misconfiguration is a critical part of cloud security strategy.
- Cloud Security assessments and hardening
- Identity and access management
- Threat detection and monitoring
- Governance and compliance processes
These controls help organisations secure cloud environments and reduce exposure to threats.
Conclusion
So, what is cloud misconfiguration?
It’s the incorrect setup of cloud systems or services that creates security vulnerabilities and exposes businesses to cyber risk.
By addressing cloud misconfiguration, organisations can:
- Protect sensitive data
- Reduce breach risk
- Improve compliance
- Strengthen cloud security posture
FAQs
What is cloud misconfiguration?
Cloud misconfiguration occurs when cloud systems or services are configured incorrectly, creating security weaknesses.
Why is cloud misconfiguration dangerous?
It can expose sensitive data, weaken security controls and allow unauthorised access.
What are common examples of cloud misconfiguration?
Public storage buckets, open ports and excessive permissions are common examples.
How do businesses prevent cloud misconfiguration?
By implementing secure configurations, monitoring systems and conducting regular security assessments.

Leave a Reply