Introduction
As cyber threats become more advanced, organisations are investing in technologies to detect and respond to attacks faster. However, with so many options available, it can be difficult to understand the differences between them.
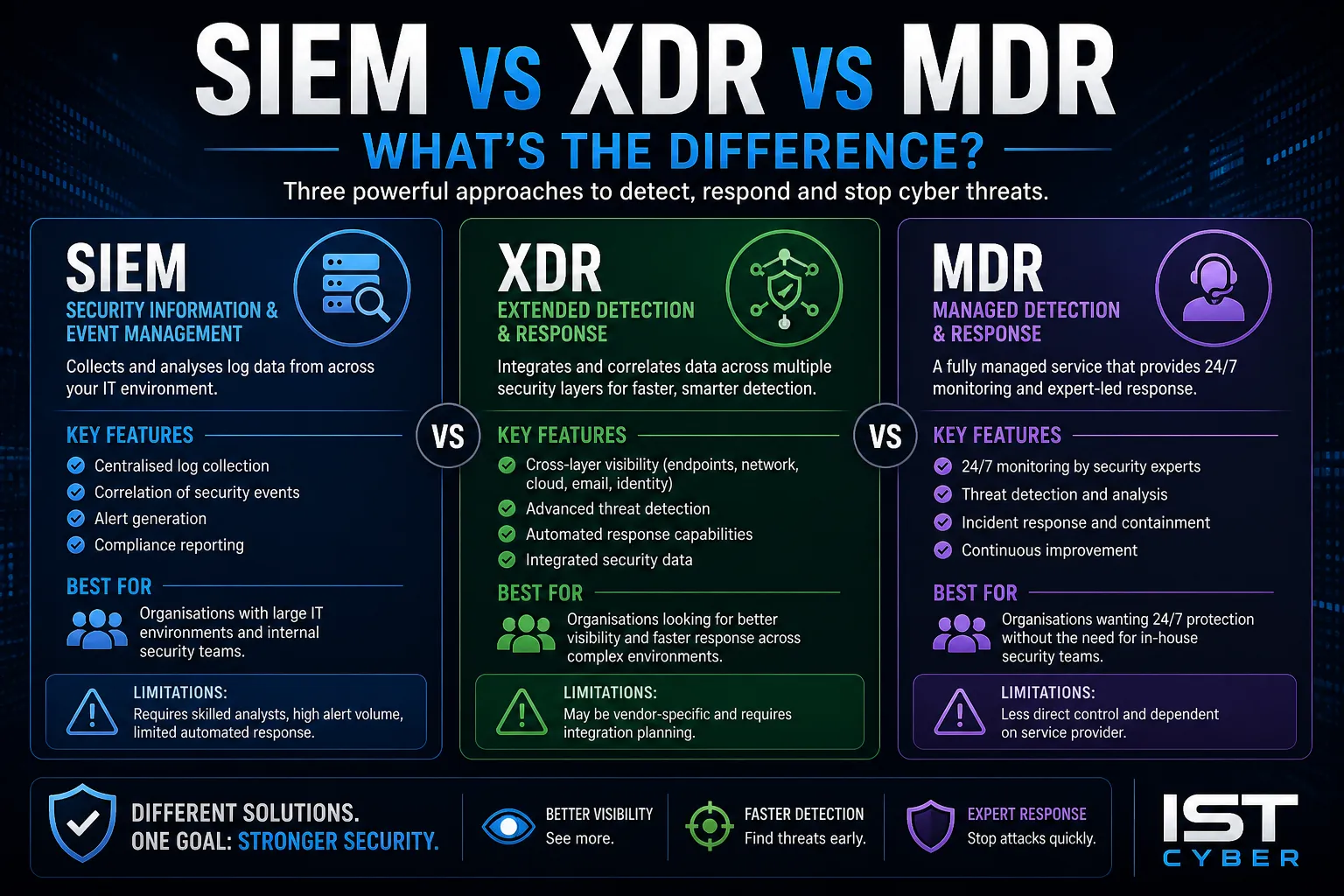
Three of the most commonly compared solutions are SIEM, XDR and MDR.
So, what is the difference between SIEM vs XDR vs MDR, and which one is right for your business?
This guide breaks down each approach, explains how they work, and helps you choose the right solution.
SIEM vs XDR vs MDR Explained
SIEM, XDR and MDR are all cyber security solutions focused on detecting and responding to threats, but they differ in how they operate and the level of service they provide.
- SIEM (Security Information and Event Management) – Collects and analyses logs from across systems
- XDR (Extended Detection and Response) – Integrates and correlates data across multiple security layers
- MDR (Managed Detection and Response) – A fully managed service that provides monitoring and response
What is SIEM?
SIEM is a platform that collects, aggregates and analyses log data from across an organisation’s IT environment.
Key features:
- Centralised log collection
- Correlation of security events
- Alert generation
- Compliance reporting
Limitations:
- Requires skilled analysts
- High volume of alerts
- Limited automated response
What is XDR?
XDR extends detection and response capabilities across multiple environments such as endpoints, networks and cloud systems.
Key features:
- Cross-layer visibility
- Advanced threat detection
- Automated response capabilities
- Integrated security data
Limitations:
- May be vendor-specific
- Requires integration planning
What is MDR?
MDR is a fully managed service that provides threat detection, monitoring and incident response.
Key features:
- 24/7 monitoring by security experts
- Threat detection and analysis
- Incident response and containment
- Continuous improvement
Limitations:
- Less direct control compared to in-house solutions
- Dependent on service provider
SIEM vs XDR vs MDR: Key Differences
| Feature | SIEM | XDR | MDR |
|---|---|---|---|
| Type | Platform | Platform | Service |
| Monitoring | Manual / Analyst-driven | Automated + integrated | Fully managed |
| Response | Limited | Automated | Expert-led response |
| Complexity | High | Moderate | Low for customer |
| Best for | Large teams with expertise | Integrated environments | Businesses needing full support |
Which One is Right for Your Business?
Choose SIEM if:
- You have an internal security team
- You need compliance reporting
- You want full control over data
Choose XDR if:
- You want better visibility across systems
- You need faster threat detection
- You prefer integrated security tools
Choose MDR if:
- You need 24/7 monitoring
- You lack internal security resources
- You want expert-led response
How This Fits into Cyber Security Strategy
SIEM, XDR and MDR are all part of a broader security operations strategy.
- Security Operations for monitoring and detection
- Incident response processes
- Threat intelligence integration
- Continuous monitoring and improvement
Choosing the right solution depends on your organisation’s size, resources and risk profile.
Conclusion
So, what’s the difference between SIEM vs XDR vs MDR?
SIEM provides visibility, XDR enhances detection across systems, and MDR delivers fully managed protection.
By understanding these differences, businesses can:
- Select the right solution
- Improve threat detection
- Respond faster to incidents
- Strengthen overall cyber security posture
FAQs
What is the difference between SIEM, XDR and MDR?
SIEM collects and analyses logs, XDR integrates detection across systems, and MDR provides a managed detection and response service.
Is XDR better than SIEM?
XDR offers more advanced detection and automation, but SIEM is still valuable for log management and compliance.
Do businesses need MDR?
Many organisations benefit from MDR if they lack in-house security expertise.
Can SIEM, XDR and MDR be used together?
Yes, they can complement each other as part of a layered security approach.

Leave a Reply